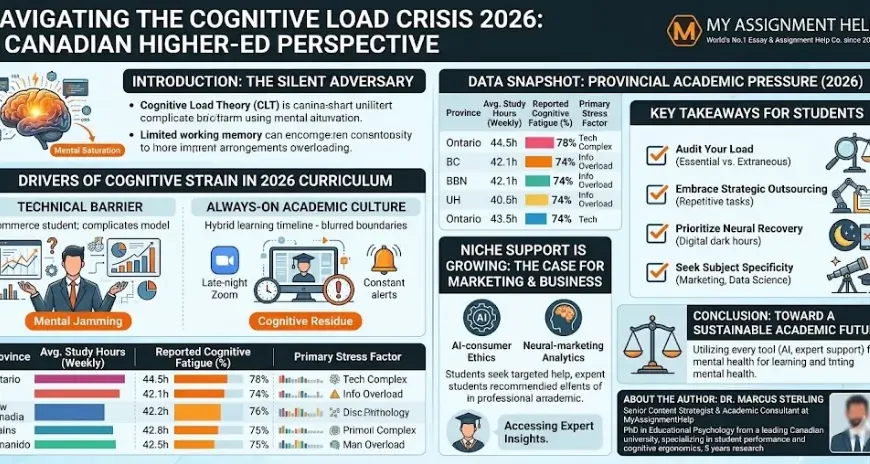
Centralization in crypto concentrates key resources, protocols, and decision power, risking single points of failure. It can speed governance but invites outages, censorship pressure, and opaque incentives that erode trust. Vigilant assessment of signals and red flags is essential. Transparent accountability, layered governance, and independent audits are proposed safeguards. The balance between security and openness remains fragile, and the stakes grow as systems scale—a tension that invites careful scrutiny and ongoing scrutiny.
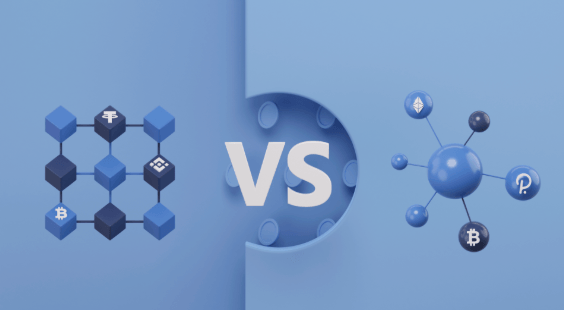
What Centralization Looks Like in Crypto Ecosystems
Centralization in crypto ecosystems manifests through concentrated control over key resources, protocols, and decision-making pathways that shape incentives, access, and governance. This concentration presents centralization tradeoffs: speed and coherence may improve, yet resilience and openness risk eroding.
Governance structures influence participation, accountability, and adaptability. A risk-aware posture highlights tradeoffs, guiding resilient designs that preserve freedom while safeguarding systemic integrity.
Concrete Harms: Outages, Censorship, and Risk Concentration
Concrete harms from centralized patterns in crypto—outages, censorship, and risk concentration—manifest as tangible disruptions to reliability, access, and trust.
Outages as outages threaten service continuity, while censorship concerns erode open participation.
Risk concentration signals and red flags highlight governance vs control tensions, demanding transparent accountability.
A governance-driven lens reduces systemic fragility, preserving freedom through deliberate, restrained, and accountable stewardship.
How to Evaluate Decentralization: Signals and Red Flags
Evaluating decentralization hinges on observable signals and notable red flags that reveal how power and decision-making are distributed.
The analysis surveys token governance processes, voting participation, and proposal pathways, distinguishing centralized bottlenecks from broad stakeholder engagement.
Validator diversity, geographic spread, and operator transparency are critical metrics.
Red flags include opaque metrics, veto power concentration, and abrupt governance changes that undermine confidence and core governance principles.
Pathways to Stronger Decentralization Without Sacrificing Security
To strengthen decentralization without compromising security, organizations can pursue layered governance that preserves core assurances while widening participation. The approach analyzes decentralization metrics to quantify risk dispersion, ensuring no single node dominates control. Emphasis on governance transparency reduces opacity, enabling verifiable accountability. Safeguards balance resilience and openness, encouraging independent audits, modular upgrades, and clear decision rights, aligning freedom with disciplined risk management.
See also: Digital Banking Transformation
Frequently Asked Questions
How Do Forks Influence Long-Term Decentralization Outcomes?
Forks influence long-term decentralization by reshaping governance, aligning incentives, and testing consensus convergence; they reveal resilience or fragility in network rules, require transparent fork dynamics, and emphasize governance-driven, risk-aware decisions for freedom-minded stakeholders.
Can Governance Tokens Create Hidden Centralization Risks?
Guarded like a wary clock, governance tokens can create hidden centralization risks. Governance centralization may emerge through concentrated token holder influence, where a few holders disproportionately shape decisions, undermining true decentralization and freedom for diverse participants.
What Role Do Auditors Play in Decentralization Assessments?
Auditors contribute to decentralization assessments by upholding auditor independence and audit transparency; they provide impartial verification of controls, risk management, and governance processes, enabling stakeholders to evaluate resilience while maintaining freedom through accountable, methodical governance practices.
How Do Off-Chain Solutions Impact Overall Security Guarantees?
Off-chain mechanisms alter risk profiles by shifting trust boundaries; however, they do not erase vulnerabilities. They modify security guarantees through separate settlement layers, requiring rigorous governance, exhaustive audits, and robust fault tolerance to maintain overall network resilience and freedom.
Are User Incentives Aligned With True Decentralization Goals?
Incentive misalignment can occur, undermining decentralization as actors chase short-term gains; governance centralization may emerge through concentrated influence. The analysis recommends transparent reward structures, multi-stakeholder oversight, and continuous stress-testing to safeguard freedom while remaining risk-aware and methodical.
Conclusion
In the ledger’s shadow, a single keystone dominates, casting long, narrow shadows across the network’s foundation. When power concentrates, resilience thins: outages loom like sudden dusk, censorship trims the branches of participation, and opaque incentives forge invisible snares. Yet with layered governance, transparent audits, and independent checks, the ecosystem can still breathe openly. A robust, decentralized architecture blooms where diverse actors hold sway, and accountability weatherproofs the system against abrupt, corrosive shifts.